How to Configure IPSec Host to Site Tunnel with Certificate
Overview
Host to Site configurations are very similar to Host to Host configurations, especially the authentication methods are the same. Added changes to the configurations are the values for rightsourceip and rightsubnets. These values will expose the listed subnets to the IPSec tunnel and will allows clients in these subnets to communicate with the host (west) node and will allow the west node to allow to communicate with clients in the listed subnets.
In case rightsourceip is used the communication between the 2 nodes will not be encrypted only communication between the west node and the subnet would be encrypted. If a value is defined, then all communication between the East and the west host will use the defined IP Address.
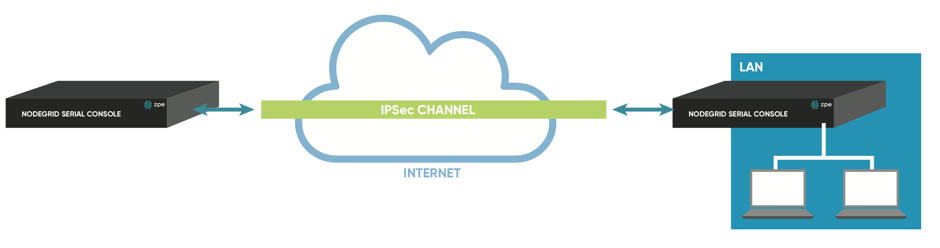
Figure 12: Host to Site Configuration Example Details
Host to Site with Certificate
- Prepare both nodes (see: How to Prepare a Nodegrid Node for IPSec)
- Get the required Certificate File for both nodes (see: How to Create Certificates for IPSec).
- Root CA certificate as .crt file
- Certificate for both nodes in .crt format
- Certificate and private key for both nodes in pkcs#12 format
- zpeca.crt
- ng-east.crt
- ng-west.crt
- ng-east.p12
- ng-west.p12
- Import the Root CertificateNote: Example executed on the west node.
- Import Intermediate Certificate Authorities if that exist
- Import the private key and certificate specific to this node
- Import the remote node certificates
- Create connection configuration file in /etc/ipsec/ipsec.d/ directory as root user
- Copy the configuration file only to the other node. The Secret File does not need to be copied in this case
- Restart IPSec service on both nodes
- Confirm that the tunnel was established
- Short information
- More Detailed Information
Example:
Format:
certutil -A -i -n "" -t "CT,," -d sql:/etc/ipsec/ipsec.d/
Example:
root@ng-west:~# certutil -A -i zpeca.crt -n "zpeca" -t "CT,," -d sql:/etc/ipsec/ipsec.d/
Format:
certutil -A -i -n "" -t ",," -d sql:/etc/ipsec/ipsec.d/
Example:
root@ng-west:~# certutil -A -i euzpeca.crt -n "euzpeca" -t "CT,," -d sql:/etc/ipsec/ipsec.d/
Format:
certutil -A -i -n "" -t "P,," -d sql:/etc/ipsec/ipsec.d/
Example:
root@ng-west:~# ipsec import ng-west.p12 -n ng-west -d sql:/etc/ipsec/ipsec.d/ Enter password for PKCS12 file: pk12util: PKCS12 IMPORT SUCCESSFUL
Format:
certutil -A -i -n "" -t "P,," -d sql:/etc/ipsec/ipsec.d/
Example:
root@ng-west:~# certutil -A -i ng-east.crt -n "ng-east" -t "P,," -d sql:/etc/ipsec/ipsec.d/
| Fields | Values | Comments |
|---|---|---|
| Connection name | <String> | |
| leftid | %fromcert | The leftid will be populated from the certificate |
| left | <IP or FQDN> of the West/Left host | Additional to an actual IP address can the following values be used. These are resolved when the service starts. %defaultgateway %eth0 |
| leftrsasigkey | %cert | Uses the RSA key of the Certificate |
| leftcert | <IDENTIFIER> | Certificate Identifier |
| rightid | %fromcert | The rightid will be populated from the certificate |
| right | <IP or FQDN> of the East/Right host | Additional to an actual IP address can the following values be used. These are resolved when the service starts. %defaultgateway %eth0 |
| rightsourceip | <INTERNAL IP TO BE USED> | IP address if the east node which should be used for the tunnel communication. This IP should belong the rightsubnet. |
| rightsubnets | <LIST OF SUBNETS> | One or multiple subnet can be defined, for each subnet a individual tunnel will be created |
| rightrsasigkey | %cert | Uses the RSA key of the Certificate |
| rightcert | <IDENTIFIER> | Certificate Identifier |
| auto | start | The setting regulates when the IPSec tunnel will be established. Following values are accepted: add (manual start), start (starts with the service), ondemand (will be established if traffic exists), ignore (connection will be ignored and not used) |
| connaddrfamily | ipv4 | Possiable values are ipv4 or ipv6 |
Format:
conn
connaddrfamily=ipv4
auto=
leftid=%fromcert
left=FQDN>
leftrsasigkey=%cert
leftcert=
rightid=%fromcert
right=FQDN>
rightsourceip=
rightsubnet=MASK>
rightrsasigkey=%cert
rightcert=
Example /etc/ipsec/ipsec.d/host-to-site-cert.conf
conn host-to-site-cert
connaddrfamily=ipv4
auto=start
leftid=%fromcert
left=192.168.50.4
leftrsasigkey=%cert
leftcert=ng-west
rightid=%fromcert
right=192.168.58.4
rightsourceip=192.168.60.4
rightsubnet=192.168.60.0/24
rightrsasigkey=%cert
rightcert=ng-east
root@ng-west:~# ipsec restart Redirecting to: /etc/init.d/ipsec stop Shutting down pluto IKE daemon 002 shutting down Redirecting to: /etc/init.d/ipsec start Starting pluto IKE daemon for IPsec: . root@ng-west:~#
root@ng-west:/etc/ipsec/ipsec.d# ipsec whack --trafficstatus 006 #4: "host-to-site-cert", type=ESP, add_time=0, inBytes=252, outBytes=252, id='C=US, ST=California, L=Fremont, CN=ng-east' 006 #3: "host-to-site-cert", type=ESP, add_time=1524106315, inBytes=0, outBytes=0, id='C=US, ST=California, L=Fremont, CN=ng-east'
root@ng-west:~# ipsec whack --status |grep host-to-site-cert ……………. 000 #4: "host-to-site-cert":500 STATE_QUICK_I2 (sent QI2, IPsec SA established); EVENT_SA_REPLACE in 27850s; newest IPSEC; eroute owner; isakmp#1; idle; import:admin initiate 000 #4: "host-to-site-cert" esp.8f05c62c@192.168.58.4 esp.33385f41@192.168.50.4 tun.0@192.168.58.4 tun.0@192.168.50.4 ref=0 refhim=0 Traffic: ESPin=252B ESPout=252B! ESPmax=4194303B 000 #1: "host-to-site-cert":500 STATE_MAIN_I4 (ISAKMP SA established); EVENT_SA_REPLACE in 2409s; newest ISAKMP; lastdpd=-1s(seq in:0 out:0); idle; import:admin initiate 000 #3: "host-to-site-cert":500 STATE_QUICK_R2 (IPsec SA established); EVENT_SA_REPLACE in 28316s; isakmp#2; idle; import:not set 000 #3: "host-to-site-cert" esp.759f48b6@192.168.58.4 esp.62dcc0e@192.168.50.4 tun.0@192.168.58.4 tun.0@192.168.50.4 ref=0 refhim=0 Traffic: ESPin=0B ESPout=0B! ESPmax=4194303B 000 #2: "host-to-site-cert":500 STATE_MAIN_R3 (sent MR3, ISAKMP SA established); EVENT_SA_REPLACE in 3116s; lastdpd=-1s(seq in:0 out:0); idle; import:not set
Related Articles
How to Configure IPSec Site to Site Tunnel with Certificate
Version 0.1 (02 May 2018) Overview Site to Site Configurations are further extension to host to site configurations. Communication is in this case expanded between multiple subnet on both sites of the connection. Subnet and communication IP addresses ...How to Configure IPSec Host to Host tunnel with Certificate
Version 0.1 (02 May 2018) Overview Host to Host configurations allow two nodes to established a tunnel between them. The encrypted communication will be limited just to the two nodes involved. Figure 11: Host to Host Configuration Example Details ...IPsec tunnel to AWS VPC with Certificates
IPsec tunnel to AWS VPC with Certificates tested on: 5.2.1, 6.0.5 AWS VPC configuration Create Certificates AWS supports multiple ways to create and manage certificates. This guide utilized AWS Certificate Manager, read AWS documentation on how the ...How to configure IPSec Host to Site tunnel with Pre-Shared Key
Version 0.1 (02 May 2018) Overview Host to Site configurations are very similar to Host to Host configurations, especially the authentication methods are the same. Added changes to the configurations are the values for rightsourceip and rightsubnets. ...How to Configure IPSec Host to Site tunnel with RSA Keys
Version 0.1 (02 May 2018) Overview Host to Site configurations are very similar to Host to Host configurations, especially the authentication methods are the same. Added changes to the configurations are the values for rightsourceip and ...